Secure it.
Send it.
The messaging app on your phone wasn't built for patient data. EMMS is. Encrypted end-to-end, never in your camera roll, works even when the recipient doesn't have the app.
The messaging app on your phone wasn't built for patient data. EMMS is. Encrypted end-to-end, never in your camera roll, works even when the recipient doesn't have the app.
Most clinical messaging today happens on WhatsApp, iMessage, SMS, and email. None of them were built for patient data. Here's what that actually looks like — and what EMMS does instead.
Every clinical photo you take on iPhone lands in your photo library, syncs to iCloud, and may surface in Memories or shared albums without warning.
Most physicians are sitting on thousands of patient images across their phone, email, and messaging apps — with no plan for when they'll be deleted.
Unencrypted channels put patient data on servers, carrier logs, and devices you don't control — and leave no meaningful audit of who saw what.
EMMS adapts to how you work. Send a quick encrypted message, or bundle images into a structured Clinical Case with context and a voice explanation — and if your recipient doesn't have the app, EMMS creates a secure link automatically.
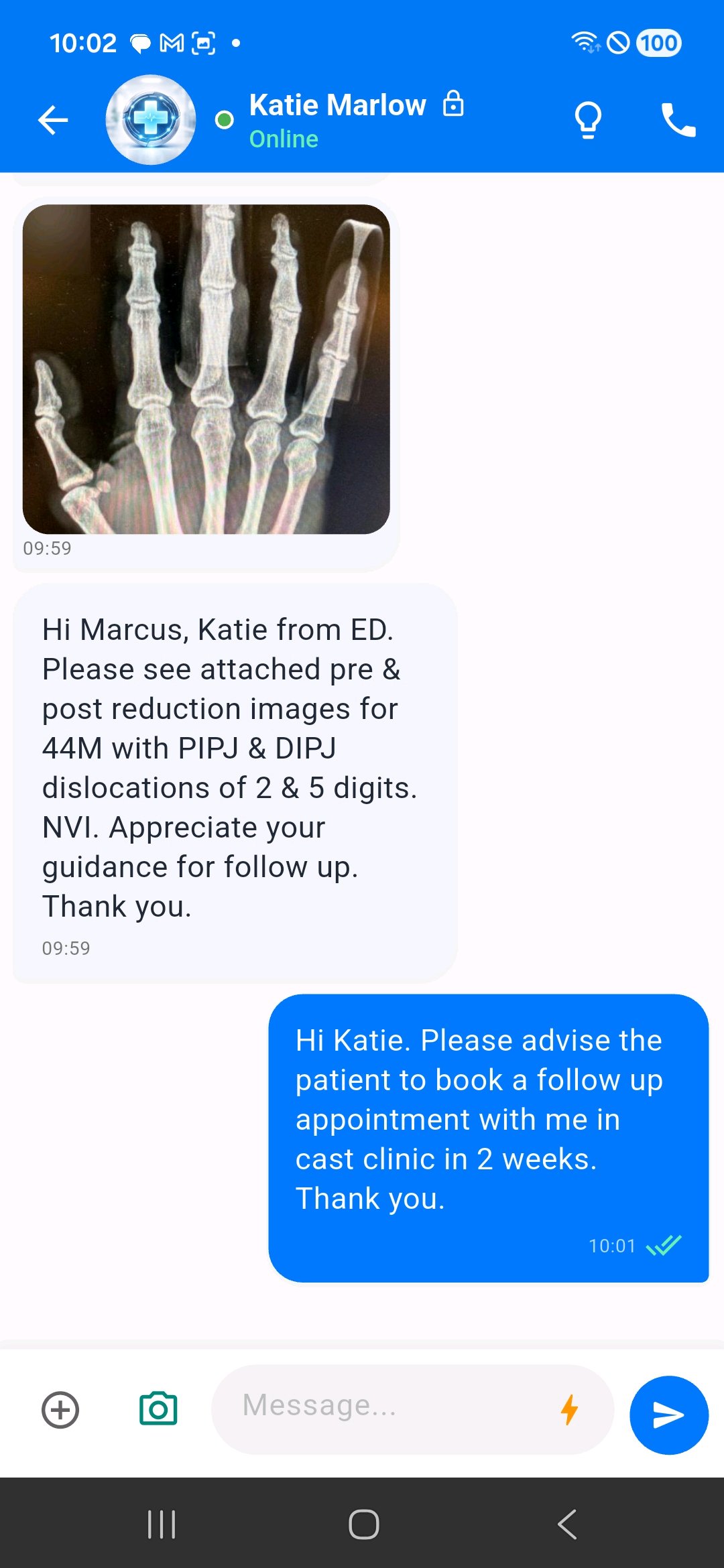
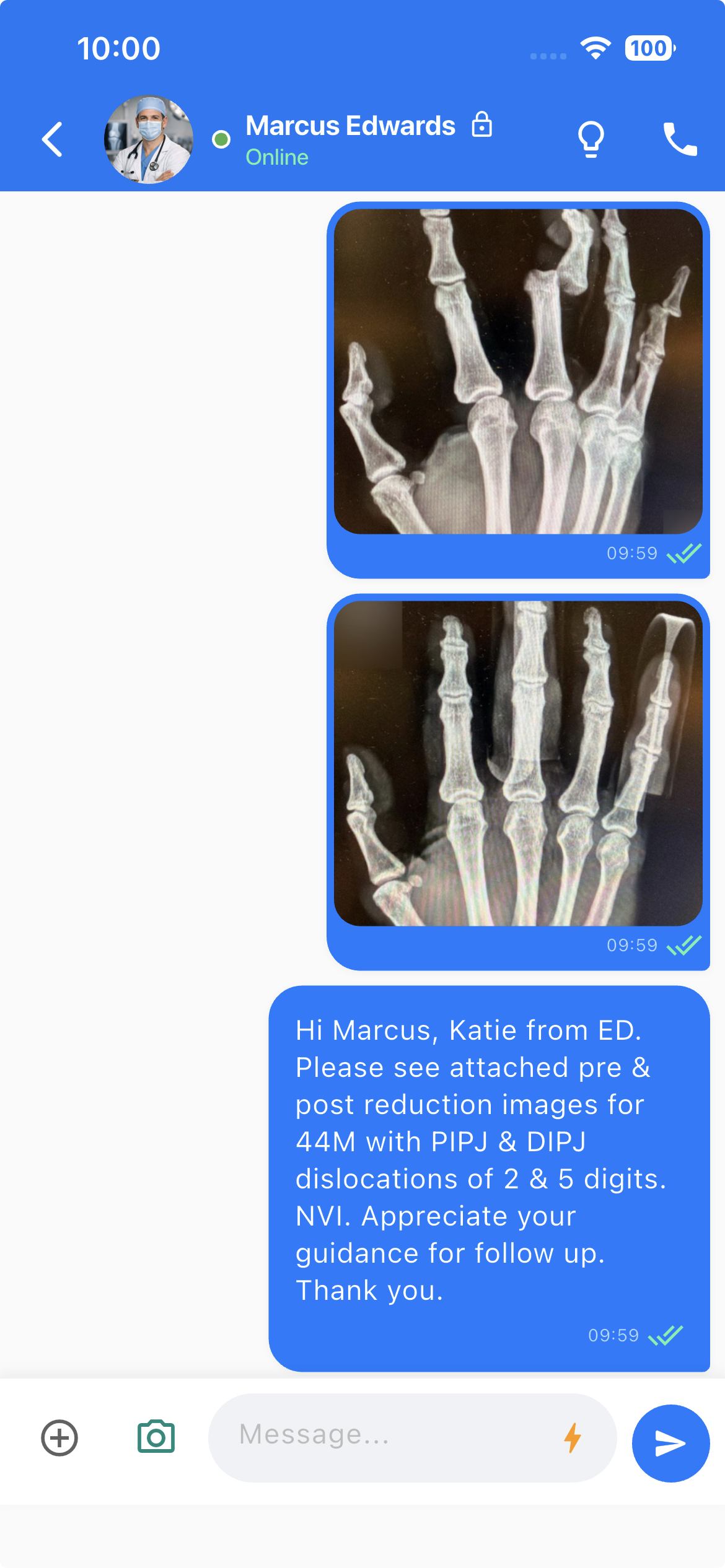
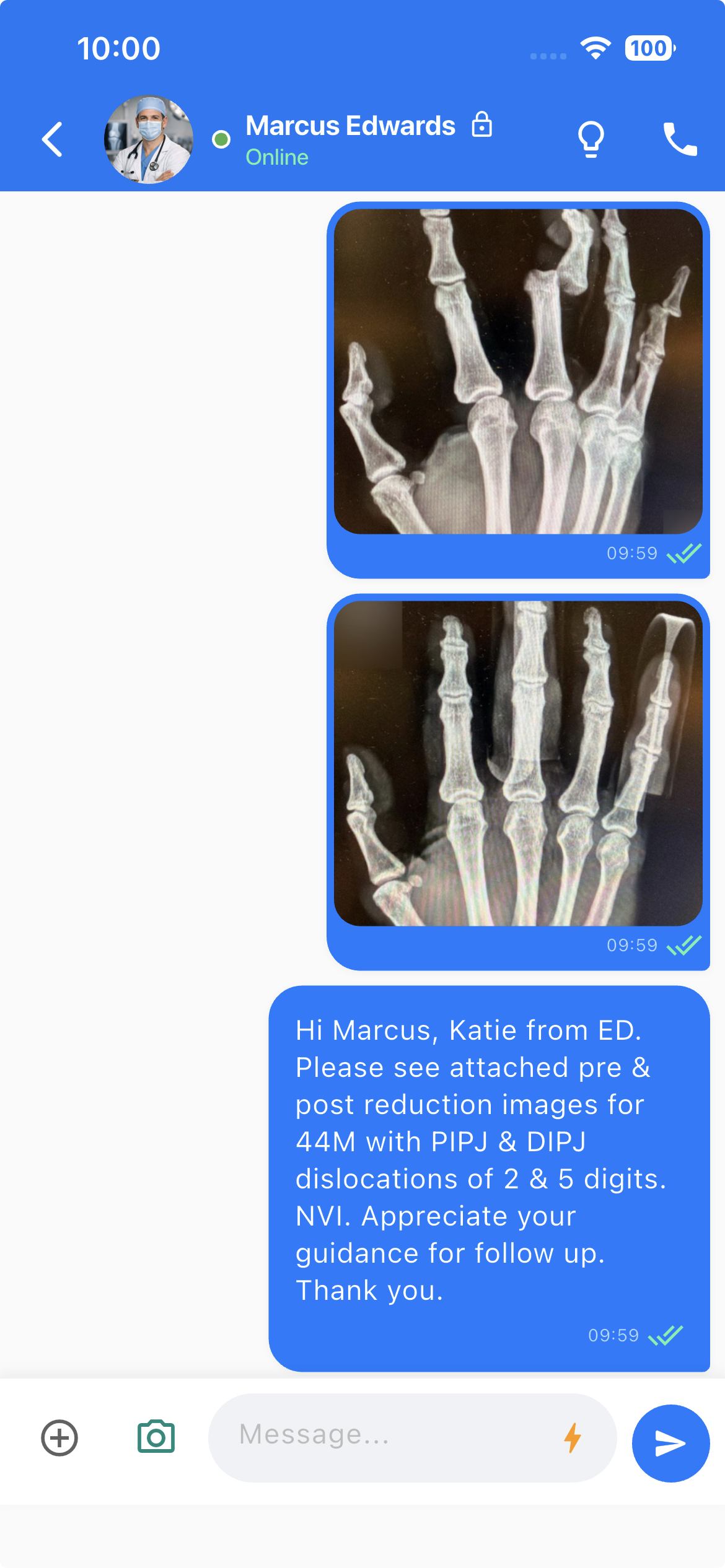
If your colleague has EMMS, it works exactly like the messaging apps you already use. Open a chat, attach files, send. Tap images to view full-screen, react, reply in-thread, see delivery and read receipts.
The difference is what's happening underneath — end-to-end encryption, no camera-roll exposure, no iCloud or Google Cloud backup. You don't think about any of it.
When a quick image isn't enough, create a Clinical Case — bundle up to 5 images with a title, context note, and a voice explanation into a single grouped message. It arrives as one organised card in the chat thread, keeping related images together rather than scattered through the conversation. Forward a case to another colleague and everything travels with it — images, metadata, and voice note.
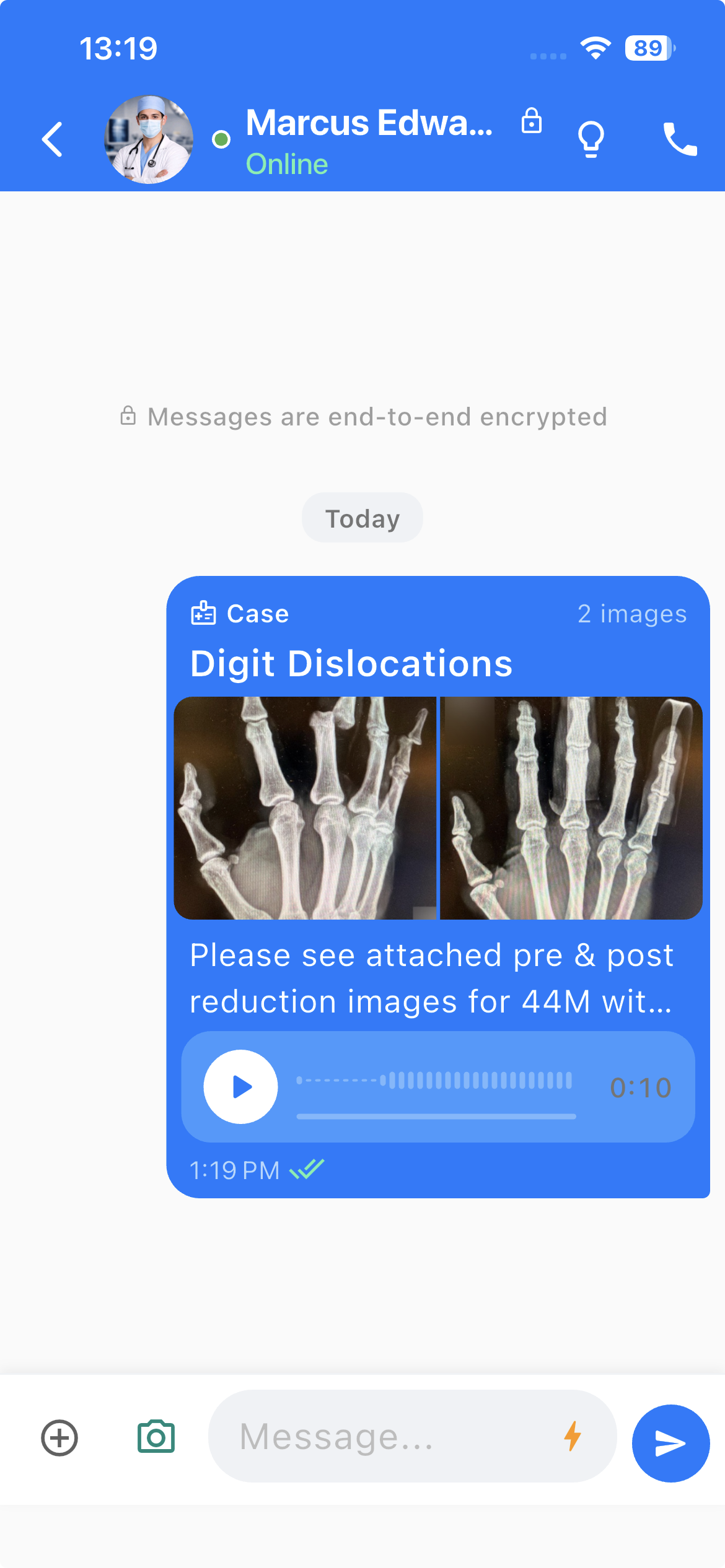


Full case detail view — title, images, context note, and voice note playback (left) · Side-by-side compare mode with synchronised zoom and pan (right)
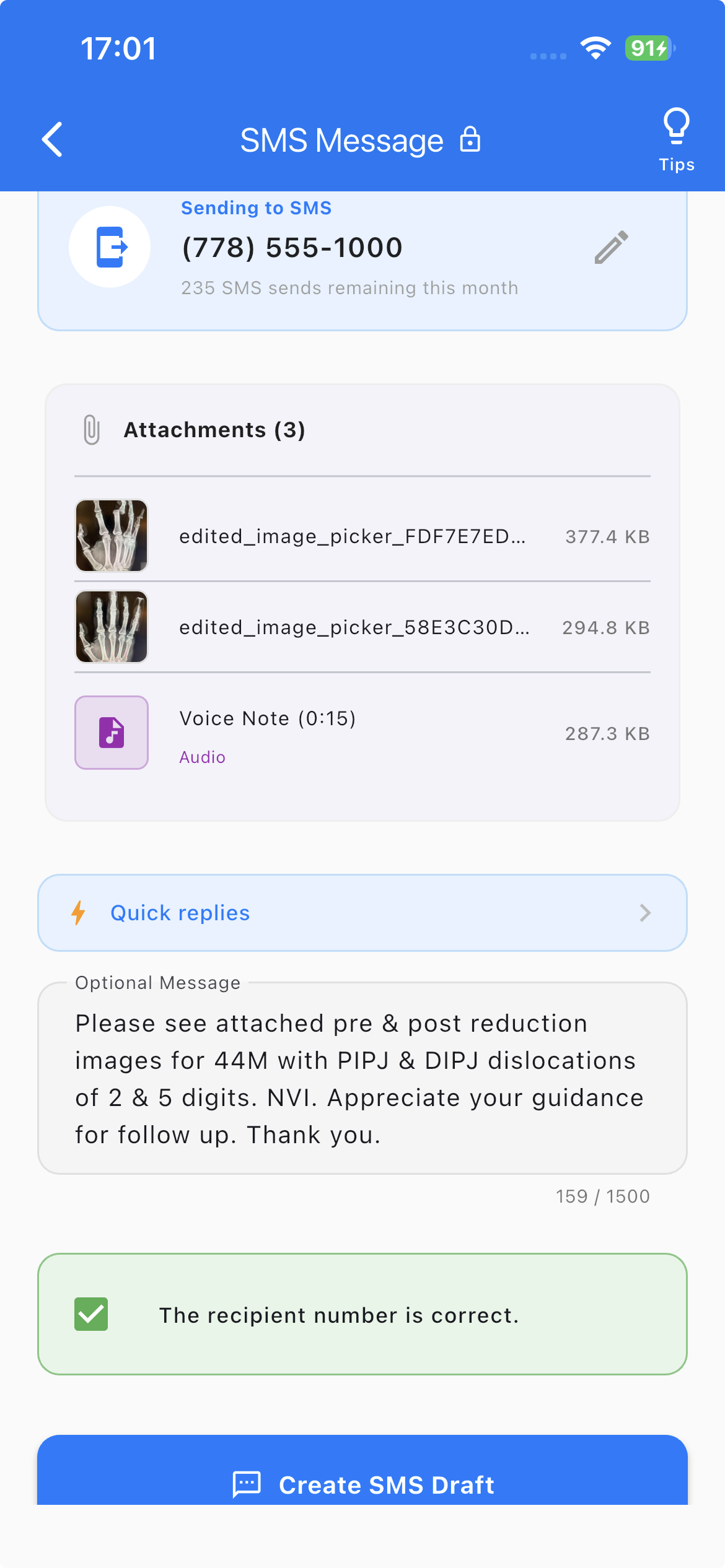
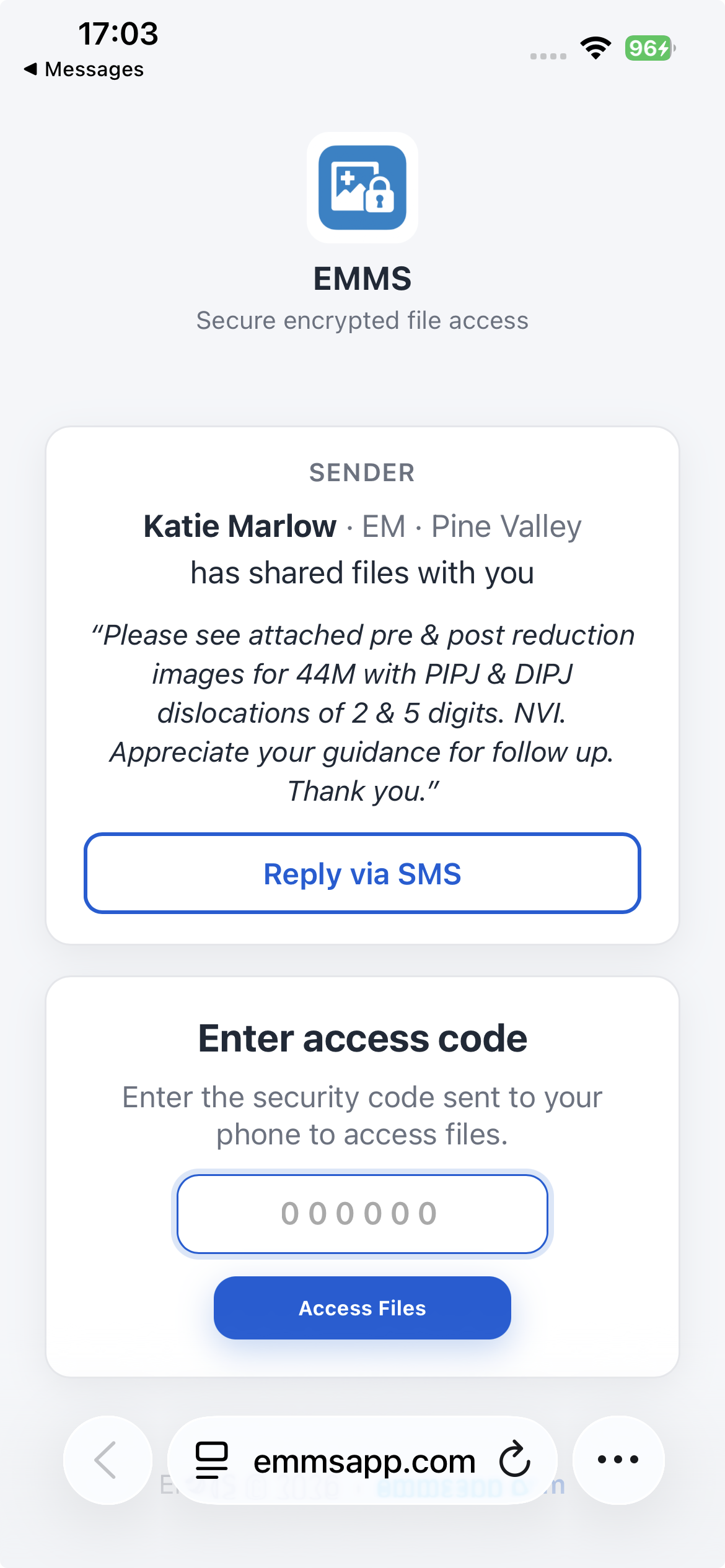
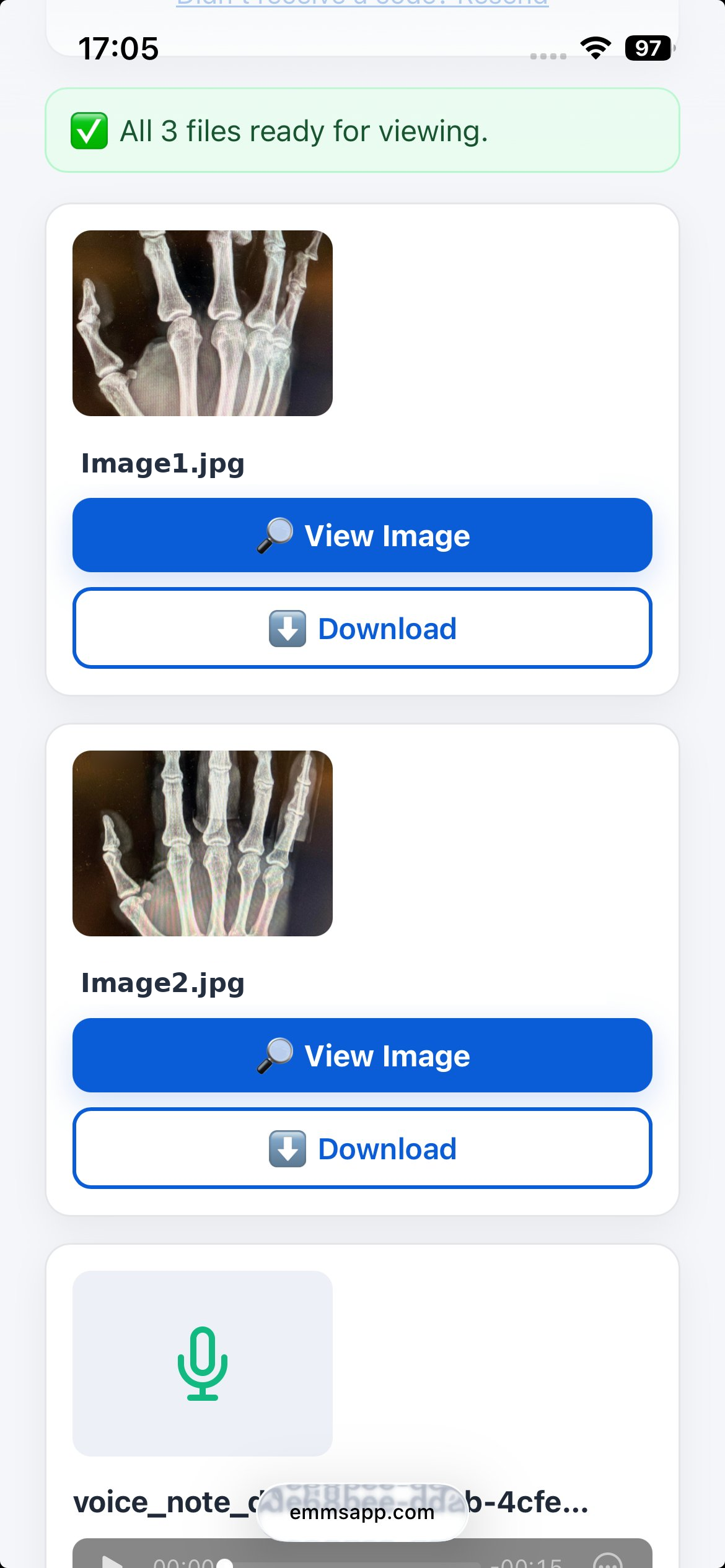
If the recipient doesn't have EMMS, the app detects this automatically, creates the encrypted secure link, and opens your phone's default messaging app with everything pre-filled. You send it yourself — EMMS never sends SMS on your behalf. The recipient verifies with a one-time code and views the files in their browser.
The biggest problem with secure messaging apps is getting the other person to install it. EMMS eliminates that entirely — and the secure link is still encrypted end-to-end.
EMMS creates the encrypted secure link and opens your phone's default messaging app with everything pre-filled. You send it yourself — EMMS never sends SMS on your behalf. The recipient taps the link, verifies their phone with a one-time code, and views the files in their browser. No app download. No account creation.
The recipient enters a time-limited 6-digit code sent to their phone. No passwords, no accounts, no email addresses. Access expires automatically.
SMS secure links are encrypted end-to-end — but the app provides deeper protection. Encryption keys live permanently on the device rather than in a temporary browser session. Files are stored in an encrypted sandbox with PIN and biometric lock, screenshot prevention, and automatic expiry. The app is the secure home for clinical files — SMS is the secure bridge when you need one.
EMMS uses a zero-knowledge architecture. Your content is encrypted on your device — our servers handle delivery but never see what's inside. No third-party service can access your message or file content.
Content is encrypted on your device before it leaves. Our server processes the delivery but never sees the content. We couldn't read it even if compelled to.
In group conversations, each member receives an individually encrypted copy of the content. There is no shared key that could compromise the group.
Files are encrypted on-device, not just in transit. Images are stored inside the app's encrypted sandbox and never appear in your photo library.
Files are removed from the server shortly after the recipient has them locally — within seconds for downloaded attachments, within hours when the recipient confirms sync, and a hard 30-day cap on anything never collected.
EMMS routes communication via hashed identifiers — we don't store your phone number on our infrastructure. When a recipient opens a secure link, our SMS provider (Twilio) delivers the verification code. Twilio never receives message or file content.
The app explicitly excludes all data from iCloud, iTunes, and Google Cloud backups. Your medical files don't silently replicate to cloud storage you haven't consented to.

Every feature was designed around clinical workflows — not adapted from a consumer messaging app.
Group up to 5 images into a single case with a title, context note, and voice explanation. Arrives as one organised card — tap to open the full case viewer with pinch-to-zoom up to 14x, brightness and contrast controls, and side-by-side compare mode with synchronised zoom and pan. Cases auto-expire by design — if a case is relevant to ongoing care, export the images to your EMR before expiry. EMMS is your transport layer, not your record of care.
Blur patient names, MRNs, and identifiers directly in the app before sending. Crop, redact, and annotate without leaving the encrypted pipeline.
Capture multiple clinical images in sequence, review and annotate each one, then batch send — all within the encrypted environment.
Browse received files by type — images, PDFs, documents — without leaving the app. Everything stays encrypted and organised.
Medical data doesn't live on a device forever. Set retention periods so files are automatically removed after a defined timeframe.
Quick verbal notes within the encrypted pipeline. Describe findings, dictate instructions, or add clinical context — all encrypted end-to-end.
Care team discussions in a single encrypted thread. Bring together GPs, specialists, and allied health providers — each member receives individually encrypted content, with no shared key that could compromise the group.
End-to-end encrypted calls between EMMS users — unlike a regular phone call, the audio never passes through a carrier network unprotected. Discuss results, coordinate care, follow up on a referral. All within the same secure platform.
Even if your device is lost, stolen, or compromised, patient data inside EMMS remains protected.
EMMS requires authentication every time it's opened. Supports fingerprint, face recognition, and PIN — independent of your device lock screen.
EMMS actively prevents screen capture and recording on supported devices. On platforms where full prevention isn't possible, the app detects capture events and alerts you.
If your PIN is entered incorrectly, EMMS enforces a cooldown period. After repeated failures, the app performs a full data wipe to protect patient information. No manual intervention needed.
All images and files are stored encrypted inside the app's isolated sandbox. Nothing is written to the camera roll, photo library, or any shared storage location.
If your phone is lost or stolen, sign in on a new device — the previous session is automatically revoked and all local data on the old device is wiped. No IT department needed.
EMMS is not a regulated health record system. Using it does not, by itself, make you compliant with PHIPA, HIA, PIPA, or your College's policies on personal health information. What it does is close the biggest practical gap most physicians have — the insecure messaging app on their phone.
Built around Canadian privacy principles. End-to-end encryption, ephemeral storage, hashed identifiers, and Canadian-only server infrastructure. The safeguards regulators and Colleges consistently expect of secure clinical communication.
Servers in Canada. Core infrastructure is hosted exclusively within Canadian borders. Limited delivery services (push notifications, SMS verification codes) operate through providers whose infrastructure may extend beyond Canada — but they never receive message or file content.
Minimal data collection. No phone numbers stored on our servers. Hashed identifiers and delivery metadata only. Firebase handles push notifications; Twilio handles SMS verification codes. Neither sees your content. RevenueCat handles subscriptions and never receives clinical data.
Zero-knowledge architecture. Content is encrypted on your device before it leaves. We can't read it, can't share it, and can't be compelled to produce content we don't hold.
You still own documentation, consent, and the medical record. EMMS is the transport layer between you and a colleague. Your EMR remains the record of care. Document clinical exchanges, obtain consent where required, and integrate images into the chart the way you normally would.
One subscription. No advertising. No data monetization. No third-party access to your content.
All prices in Canadian dollars. EMMS is funded by the physicians who use it — not by advertisers, data brokers, or third parties. No one else pays us, which means no one else has a claim on your data.
No IT setup. No admin provisioning. No email account required. Download the app, verify your phone number, and start sending — in under two minutes.
Quick answers to the questions we hear most from physicians and IT teams.